Cant Miss Takeaways Of Tips About Is It Safe To Run A Tor Relay
![[torrelays] EFF's University Tor Relay Campaign Torrelays [torrelays] EFF's University Tor Relay Campaign Torrelays](https://forum.torproject.org/uploads/default/optimized/2X/e/e9da3a83569d27c425855d7291e7e3e1da0dc4c0_2_1024x512.jpeg)
[torrelays] EFF's University Tor Relay Campaign Torrelays
Unveiling the Mystery
1. The Tor Network
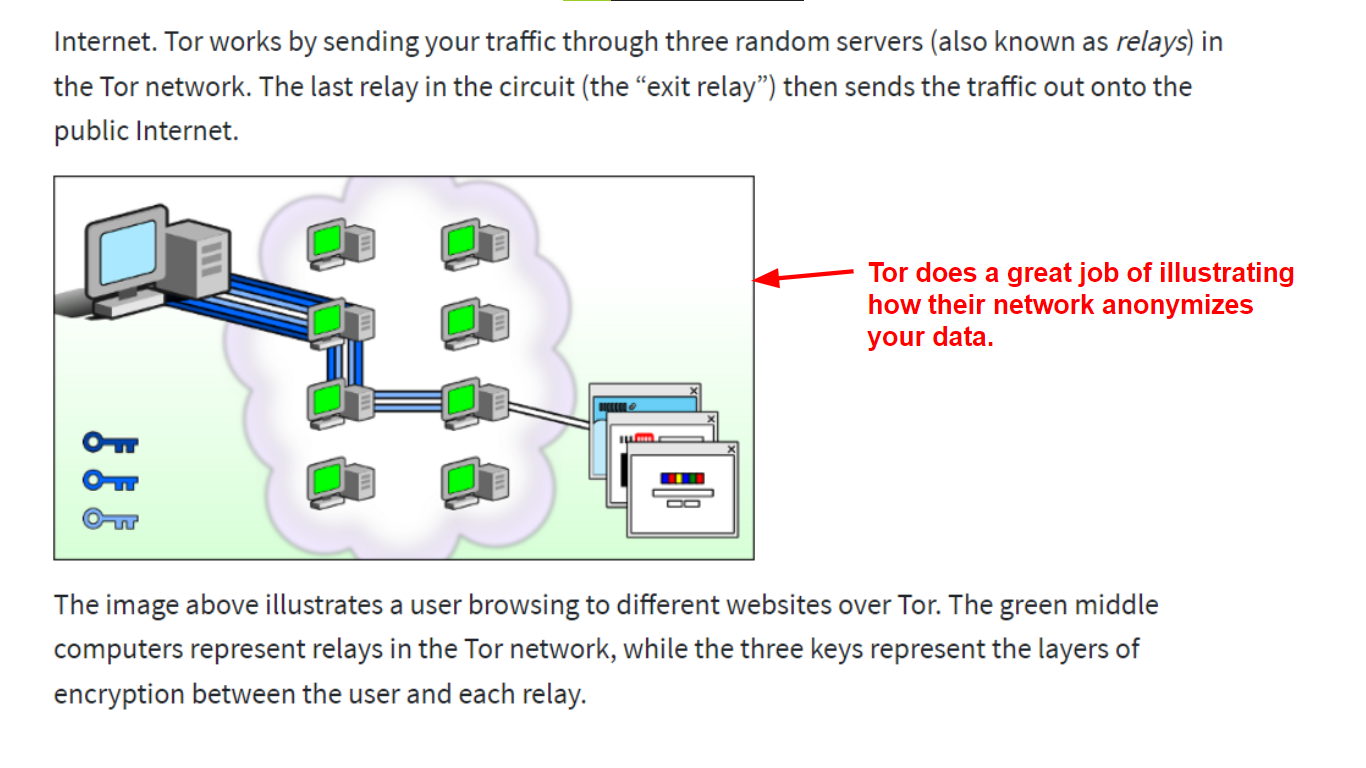
So, you're pondering the question: "Is it safe to run a Tor relay?" That's a good question, and one worth exploring. Before we dive into the nitty-gritty (oops, almost slipped!), let's quickly recap what Tor is all about. Think of it as the internet's cloak of invisibility. It's a network designed to provide anonymity by routing internet traffic through a series of volunteer-operated servers, making it difficult to trace online activity back to a specific user. Think of it like a digital game of telephone, but instead of gossip, it's data getting passed around.
Tor relies on these volunteer servers, called relays, to function. Without them, the whole anonymity apparatus falls apart. These relays are the unsung heroes of the internet privacy movement. They are people like you and me, running software that helps bounce internet traffic around the world, obfuscating its origin and destination. That's where you come in. You're considering joining their ranks by running your own relay. But, is it a good idea? Let's find out.
Imagine you're running a popular coffee shop, and people keep using it as a meeting point to discuss sensitive topics. As the owner, you're not involved in their conversations, but you're providing the space where it happens. A Tor relay is quite similar in concept. You're providing bandwidth, but you have no insight into the content being transmitted. It's just encrypted data flowing through your server.
Essentially, a Tor relay acts as a middleman. It receives encrypted data, passes it on to another relay, and eventually, that data exits the Tor network to reach its destination. This process makes it remarkably difficult to trace the origin of the data. The more relays there are, the stronger and more resilient the Tor network becomes. Your participation, in effect, helps protect the privacy of users worldwide.

Privacy Toolkit For Librarians Ppt Download
Potential Risks and Concerns
2. Addressing the "Am I Responsible?" Question
Okay, let's address the elephant in the room — the potential risks. The biggest concern that pops into most people's minds is: "If questionable activity goes through my relay, am I responsible?" It's a valid question, and the answer is somewhat nuanced. Legally, in most jurisdictions, you are generally not responsible for the content that passes through your relay, as long as you're simply providing the service and not actively participating in any illegal activities. Think of it like this: the postal service isn't responsible for the contents of every letter it delivers.
However, that doesn't mean you're completely immune to scrutiny. Law enforcement might, in theory, investigate a relay if it's suspected of being involved in illegal activity. This is where a good legal counsel comes in handy. The key is to operate transparently and in compliance with local laws. This includes keeping your software up-to-date and maintaining proper security practices on your server.
Another potential risk is the possibility of being flagged or blocked by certain websites or services. Since Tor is often used to circumvent geographical restrictions or avoid tracking, some websites automatically block traffic originating from Tor exit nodes (relays that directly connect to the regular internet). This might affect your own browsing experience if you share the same IP address as your relay. Luckily, there are ways to mitigate this, such as configuring your relay to be a middle relay only, which doesn't directly connect to the internet.
Resource consumption is another factor to consider. Running a Tor relay requires bandwidth and processing power. You'll need a stable internet connection and a server that can handle the traffic load. This can translate to increased electricity bills and potential performance slowdowns on your other devices if you're running the relay on a shared connection. Before setting up a relay, evaluate your resources and ensure you can comfortably handle the demands.
Mitigating Risks and Staying Safe
3. Tips and Best Practices
So, you're still interested in contributing to the Tor network? Awesome! The good news is, there are plenty of ways to mitigate the risks and make running a relay as safe as possible. First and foremost, keep your software updated. This includes the Tor relay software itself, as well as your operating system and any other software running on your server. Security updates often patch vulnerabilities that could be exploited by malicious actors.
Secondly, configure your relay properly. The Tor Project provides detailed documentation and guides on how to set up and configure your relay securely. Pay close attention to these instructions and follow them carefully. Consider setting bandwidth limits to prevent your relay from consuming too much of your internet connection. You can also configure your relay to be a "middle relay" only, which doesn't directly connect to the internet and reduces the risk of being associated with exit traffic.
Thirdly, monitor your relay's performance and logs. Keep an eye on your server's resource usage and check the Tor relay logs for any unusual activity. This can help you identify and address potential problems before they escalate. There are also various monitoring tools available that can help you track your relay's performance and security.
Consider consulting with a legal professional. While you are generally not responsible for the traffic passing through your relay, it's always a good idea to seek legal advice to understand your rights and responsibilities in your specific jurisdiction. This can provide you with peace of mind and help you navigate any potential legal challenges.

The Benefits of Running a Tor Relay
4. Contributing to a Worthy Cause
Okay, we've talked about the risks, but let's not forget the benefits! Running a Tor relay is a fantastic way to contribute to a more private and secure internet. You're helping to protect the anonymity of journalists, activists, whistleblowers, and ordinary citizens who rely on Tor to communicate securely and access information freely.
By running a relay, you're strengthening the Tor network and making it more resilient to censorship and surveillance. The more relays there are, the more difficult it becomes for governments and other entities to block or monitor Tor traffic. You're essentially becoming a digital freedom fighter, fighting for privacy and freedom of expression online.
Running a Tor relay can also be a learning experience. You'll gain a deeper understanding of how the internet works, how anonymity networks function, and the importance of privacy in the digital age. It's a great way to expand your technical knowledge and contribute to a community of like-minded individuals who are passionate about internet freedom.
Ultimately, running a Tor relay is an act of civic responsibility. You're contributing to a public good that benefits everyone. It's a small way to make a big difference in the world. Think of it as planting a tree in the digital forest — it might not seem like much on its own, but collectively, these trees can create a thriving and vibrant ecosystem.
Alternatives to Running a Full Relay
5. Still Want to Help?
Perhaps the potential risks associated with running a full relay are a bit too much for you right now. That's perfectly understandable! The good news is, there are other ways to support the Tor network without running a full relay. One option is to run a Tor bridge. Bridges are relays that aren't publicly listed in the Tor directory, making them more difficult to block. They're often used in countries where Tor is censored.
Another option is to simply use Tor as a user. By browsing the internet through Tor, you're contributing to the network's traffic and helping to obfuscate the activities of other users. You can also donate to the Tor Project, which helps fund the development and maintenance of the Tor software and network infrastructure. Every little bit helps!
You can also become a Tor advocate. Spread the word about Tor and its importance to your friends, family, and colleagues. Educate them about the benefits of online privacy and security. The more people who understand and support Tor, the stronger the network will become.
Regardless of how you choose to contribute, your support for Tor is valuable. Whether you're running a full relay, a bridge, using Tor as a user, donating to the Tor Project, or simply spreading the word, you're helping to protect privacy and freedom of expression online. Every action, no matter how small, contributes to a more secure and open internet for everyone.

The New Guide To Running A Tor Relay Project
FAQ
6. Q
A: It can, but it doesn't have to. You can configure your relay to limit the amount of bandwidth it uses, preventing it from hogging your entire connection. Experiment with different bandwidth limits to find a balance between contributing to the Tor network and maintaining a good browsing experience for yourself.
7. Q
A: Absolutely! Many Tor relays are run from home connections. Just make sure you have a stable internet connection and sufficient bandwidth. Also, check your internet service provider's terms of service to ensure that running a relay is permitted.
8. Q
A: As long as you're simply providing the service and not actively participating in any illegal activities, you're generally not responsible. However, law enforcement might investigate. It's a good idea to keep your software up-to-date, monitor your logs, and consult with a legal professional if you have any concerns.
9. Q
A: Basic technical skills are helpful, but you don't need to be a computer expert. The Tor Project provides detailed documentation and guides to walk you through the setup process. There are also many helpful online communities where you can ask questions and get support.