Out Of This World Tips About What Is Step 5 Of The RM Process

Understanding the RM Process
1. What's This "RM Process" Anyway?
Alright, let's break down this "RM Process" thing. If you've stumbled upon this article, chances are you're trying to figure out what step five of some risk-related activity is. Don't worry, we'll untangle it. The RM process, in most contexts, usually refers to Risk Management. It's a structured way of identifying, assessing, and controlling risks within a project, organization, or even your personal life (though you might not call it that when you're deciding whether to try that questionable street food!).
Risk management isn't about eliminating all risks, because let's face it, that's impossible. It's about understanding potential threats and opportunities and deciding how to respond to them intelligently. Think of it as preparing for a hike: you check the weather, pack water, and maybe bring a map. You haven't eliminated the risk of getting lost or thirsty, but you've minimized them.
The beauty of a structured risk management process is that it helps you make better decisions based on data and careful consideration, instead of just gut feelings. Sure, sometimes your gut is right, but wouldn't you rather have a well-thought-out plan to back it up?
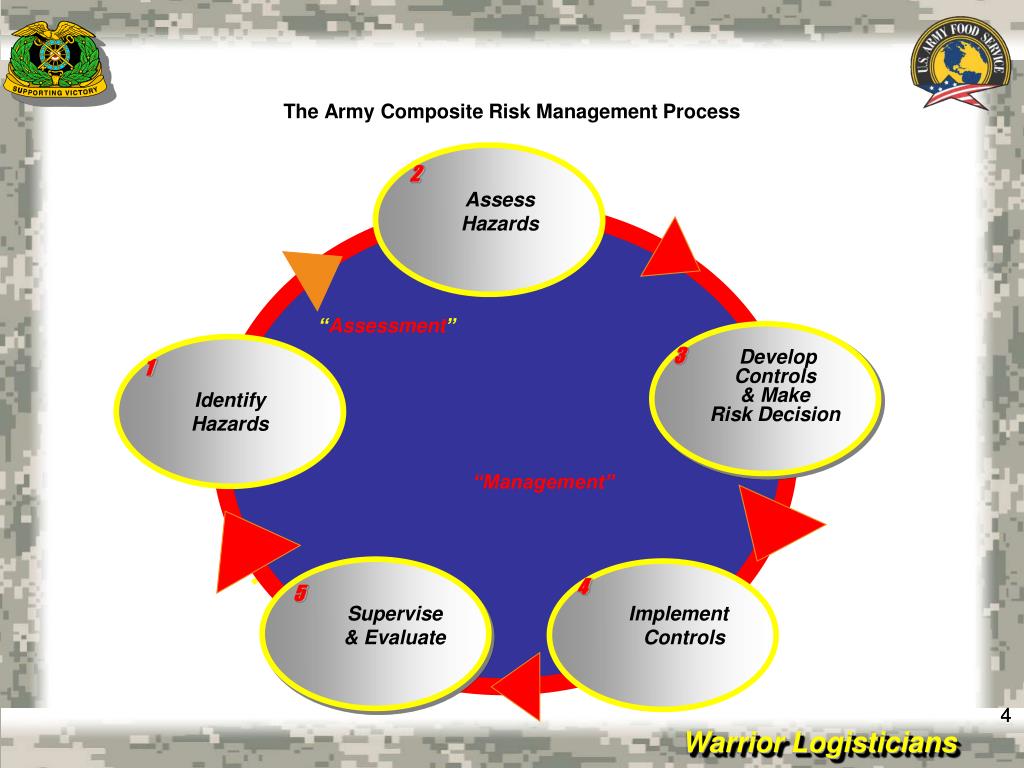
Different organizations and industries might have slightly different variations of the RM process, but the core principles remain the same. It's a cycle of continuous improvement, constantly adapting to new information and changing circumstances. So, what's this magical step five we're all here to learn about?

The RM Process (see Online Version For Colours) Download Scientific
Step 5
2. Putting Your Plan into Motion
So, you've identified the risks, analyzed them, prioritized them, and developed a plan to address them. Guess what? Now you actually have to do something! Step 5 of the RM process is all about Implementing the Risk Response. This is where your well-laid plans meet reality.
This stage involves taking the actions you defined in your risk response plan. Maybe that means buying insurance, implementing new security protocols, training your staff, or developing a backup plan for a critical system. The specific actions will depend on the nature of the risks and the chosen response strategy.
Consider it like this: you've diagnosed the problem (the risk) and prescribed a treatment (the risk response). Now you need to administer the medicine! This isn't a passive activity; it requires active management, coordination, and communication. Everyone involved needs to understand their roles and responsibilities in implementing the risk response.
Think of it as assembling a complex piece of furniture. You have the instructions (the risk response plan), the parts (the resources), and the tools (the processes). But you still need to put everything together correctly to avoid a wobbly table. Implementing the risk response is where you actually build the "wobbly-table-avoidance" mechanism.

Risk Management Process 5 Essential Steps Sprinto
Important Considerations During Implementation
3. Smooth Sailing (Hopefully!)
Implementing the risk response isn't just about ticking boxes and crossing items off a list. It's about doing it effectively and efficiently. Several factors contribute to a successful implementation.
First, communication is key. Make sure everyone involved understands the plan, their roles, and the importance of the risk response. Transparency is crucial for building trust and cooperation.
Second, resource allocation is critical. Ensure you have the necessary budget, personnel, and equipment to execute the plan effectively. Skimping on resources can compromise the effectiveness of the risk response.
Third, monitoring and tracking progress is essential. Keep an eye on key performance indicators (KPIs) to ensure the risk response is achieving its intended objectives. If things aren't going as planned, be prepared to make adjustments.
Finally, don't forget about documentation. Keep a record of all actions taken, decisions made, and results achieved. This documentation will be invaluable for future risk management efforts. Think of it as building a library of lessons learned, so you don't repeat the same mistakes twice.
Five Risk Management Kpis For Effective Contract Comp Vrogue.co
Beyond Implementation
4. The Journey Doesn't End Here
While Step 5 focuses on implementing the risk response, it's crucial to understand that risk management is an ongoing process. After implementation, you enter the monitoring and control phase, where you track the effectiveness of your risk responses and make adjustments as needed.
Monitoring involves continuously observing the environment for new risks or changes in existing risks. Control involves taking corrective actions when deviations from the plan occur. This could involve modifying the risk response, re-evaluating the risk assessment, or even developing new risk responses.
Imagine you've installed a new security system (the risk response) to protect your home from burglars. You wouldn't just install it and forget about it, would you? You'd monitor the system to ensure it's working properly, and you'd adjust it as needed based on changes in your environment (e.g., new security threats). The same principle applies to risk management in any context.
The continuous cycle of identification, assessment, response, implementation, and monitoring ensures that the risk management process remains effective over time. This cyclical approach allows for ongoing improvement and adaptation to changing circumstances. This active form of risk management helps keep you stay one step ahead.'
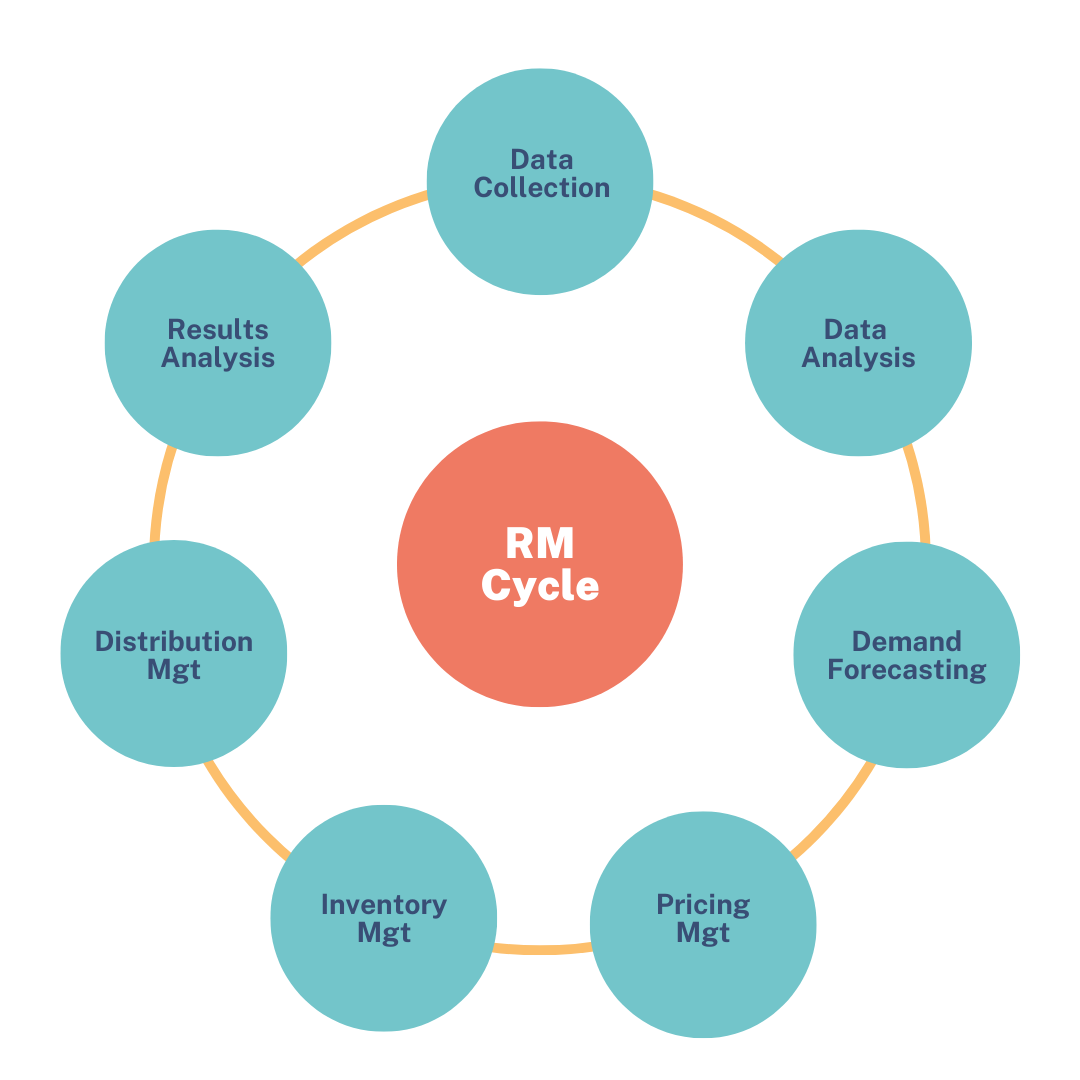
The Purpose Of Revenue Management And How To Implement It Beonprice
A Practical Example
5. Bringing It All Together
To illustrate step 5, let's consider a cybersecurity risk. Suppose a company identifies a risk of a data breach due to weak passwords. After assessing the risk, they decide to implement a policy requiring employees to use strong, unique passwords and enable multi-factor authentication (MFA).
Implementing this risk response (Step 5) involves several actions: The IT department needs to configure the systems to enforce password complexity requirements and enable MFA. They also need to communicate the new policy to employees and provide training on how to create strong passwords and use MFA.
During implementation, the company might encounter challenges, such as resistance from employees who find the new policy inconvenient. To address this, they might offer incentives for compliance or provide additional support to employees who struggle with the new technology. The key is to adapt and address challenges during this phase so that the risk response is effective.
After implementation, the company would continuously monitor the effectiveness of the password policy and MFA. This might involve tracking the number of successful phishing attempts, monitoring user accounts for suspicious activity, and conducting regular security audits. This ongoing effort ensures the cybersecurity measures stay current and effective.

Frequently Asked Questions (FAQs)
6. Your Burning Questions Answered
Let's address some common questions about the RM process and Step 5 in particular.
Q: What happens if the risk response doesn't work?
A: That's why you have monitoring and control in place! If the risk response isn't effective, you need to reassess the risk, identify the reasons why the response failed, and develop a new or modified response. Risk management is an iterative process.Q: Is risk management only for big companies?
A: Absolutely not! Risk management principles can be applied to any situation, big or small. Even individuals can use risk management techniques to make better decisions in their personal lives (e.g., managing finances, planning a trip).Q: Who is responsible for implementing the risk response?
A: It depends on the specific risk and the organization. Typically, it's a shared responsibility involving various stakeholders, including project managers, department heads, and individual employees. Clear roles and responsibilities should be defined in the risk response plan.Q: What's the biggest challenge in implementing risk responses?
A: Often, it's resistance to change. People may be reluctant to adopt new procedures or technologies, especially if they perceive them as inconvenient or burdensome. Effective communication, training, and leadership are essential for overcoming this challenge.